In 2026, demand for cybersecurity professionals is soaring, and ethical hacking skills have never been more important. As cyberattacks grow more frequent and sophisticated, companies and governments are urgently seeking trained white-hat hackers who can protect digital assets. This trend is particularly evident in Delhi’s South region — students searching for ethical hacking institute in Sangam Vihar or cyber security course in Sangam Vihar find themselves in high demand local training hubs. Sangam Vihar Bus Depot and nearby Tughlakabad are well-connected areas in South Delhi, making it convenient for aspiring cyber warriors. At EINITIAL24, we offer comprehensive ethical hacking coaching near the Sangam Vihar Bus Depot, ensuring that local students can launch a high-growth cybersecurity career without long commutes.
Why Ethical Hacking is a High-Demand Career in 2026
Cyber threats have exploded in recent years, fueled by digital transformation and emerging technologies. Today’s hackers use advanced tools and even artificial intelligence to find vulnerabilities, which means organizations must stay ahead. For example, analysts note that AI-driven attacks have surged, with many breaches occurring in record time. The average time it takes for cybercriminals to breach a system has dropped dramatically, and attacks leveraging artificial intelligence have increased. In fact, one report found a 65% faster breakout time year-over-year, along with an 89% jump in AI-enabled attacks. These trends underline the growing battlefield that ethical hackers must defend.
At the same time, businesses and governments are pouring resources into cybersecurity. Regulatory mandates and data protection laws (like India’s new Digital Personal Data Protection Act) require companies to hire dedicated security teams. Nearly all major Indian banks, healthcare firms, and government agencies now maintain 24/7 security operations, making cybersecurity staffing essential. Industry data suggests that by 2026 India will need on the order of 1.5 million cybersecurity professionals, yet currently only a fraction of that number are formally trained. This severe talent gap means freshers with even basic certifications are being snapped up by employers at higher salaries than ever before.
For individuals, this creates an outstanding career opportunity. Ethical hackers — sometimes called penetration testers or security analysts — play a critical role in protecting data and networks. The world’s largest companies, including tech giants and financial institutions, highly prize professionals who can think like hackers to find and fix security holes. Because of this, ethical hacking is viewed as a recession-resistant career. Salaries for trained cybersecurity experts are rising faster than most IT fields. In 2026, an entry-level ethical hacker in India can expect roughly ₹4–7 lakhs per annum, while mid-level specialists may command ₹8–15 lakhs. Senior experts and consultants (especially those with niche skills in cloud or AI security) can earn well above ₹20 lakhs. Globally, opportunities abound too — a certified ethical hacker often finds roles in multinational firms, defense projects, and even as freelance security consultants.
Demand for Cyber Security Professionals
The need for skilled defenders keeps accelerating. Surveys of Indian enterprises and service providers report a “sharp shortage” of qualified security staff. For example, more than 70% of firms say it’s hard to fill cyber roles, and many that do hire discover new hires lack practical skills. This has prompted companies to increase budgets and training programs: nearly all organizations are raising cybersecurity spending year over year. One industry forecast projects India’s cybersecurity market growing over 18% annually, reaching around ₹280 billion. Remarkably, over 90% of Indian companies are expanding their security teams this year — over 30% of those by more than 15%. In metro hubs like Bangalore, demand is so fierce that security job listings grew over 200% compared to just a few years ago.
Delhi, with its mix of government, finance, and tech industries, is a hotspot for security jobs. Local universities and training centers are responding by opening new programs in ethical hacking and penetration testing. The Sangam Vihar area benefits from this trend: students here can join the cyber workforce quickly by enrolling in nearby courses. As one cybersecurity career guide notes, employers in banking, healthcare and e-commerce are all actively hiring ethical hackers. In fact, Banking, Financial Services, and Insurance (BFSI) is now India’s single largest cybersecurity employer sector. Government and defense agencies also recruit ethical hackers for sensitive projects. With cloud computing and Internet of Things (IoT) technologies spreading, even traditional industries (manufacturing, retail, logistics) need security experts.
Industries Hiring Ethical Hackers
Nearly every industry today needs cyber protection. Some key sectors hiring ethical hackers include:
- Banking and Finance — Protecting customers’ money and data is critical. Banks and fintech companies hire hackers to test ATMs, online banking portals, and mobile apps.
- Healthcare — Patient records and medical devices are lucrative targets. Hospitals and healthtech firms bring in security experts to safeguard health data and comply with privacy laws.
- Government and Defense — National critical infrastructure (power grids, defense systems, public databases) must be secured. Ethical hackers help government agencies fortify networks and prepare for cyberwarfare.
- Technology and IT Services — Tech companies, ISPs, and software developers need hackers to evaluate their own products and services. Many IT firms run dedicated pentesting teams.
- E-Commerce and Retail — Online shopping and payment systems handle customer credentials. E-commerce giants employ hackers to protect payment gateways, customer info, and back-end servers.
- Telecommunications — Mobile networks and telecom infrastructure must be resilient. Telcos hire security pros to prevent outages and intercept attempts to disrupt communications.
In short, as one career advisory points out, “ethical hackers are in demand across nearly every sector.” The digital economy cannot function without people who understand hacking from the inside. By training as an ethical hacker, you open doors in any of these fields. Our students at EINITIAL24 have gone on to join leading banks, IT firms, and security firms after graduation.
Average Salary of Ethical Hackers in India
Salaries for ethical hackers are very competitive. As of 2026, a fresh graduate or newcomer to the field (with a certification like CEH) can expect roughly ₹4–7 lakhs per annum in India. This range varies by city and employer; for example, larger firms in Delhi or Bangalore may start at the higher end. With a few years of experience, salaries typically jump into the ₹8–15 lakh range. Seasoned professionals with 5–10 years’ experience or specialized skills (like cloud security or AI defense) often earn upwards of ₹20–30 lakhs, and can even exceed ₹40 lakhs as consultants or architects in top companies. Overall, one industry report puts the average annual ethical hacker salary around ₹5.2 lakhs, but emphasizes that this depends heavily on location, company, and specific skill set. In comparison, government cybersecurity roles may pay slightly less but come with long-term benefits.
To put it in perspective, ethical hacking careers now rival or exceed many traditional IT salaries. India’s average IT salary growth is around 8–10% per year, but cybersecurity specialists often see 10–15% annual jumps. In local terms, Delhi-area companies often pay competitive packages for certified experts. According to surveys, Delhi government and corporate sectors might offer ₹5–9 lakhs even for early-career roles, with larger firms going higher. Meanwhile, freelance ethical hackers (bug bounty hunters, independent consultants) can sometimes earn even more by working with international clients. The clear takeaway: trained ethical hackers are well compensated, reflecting the critical importance of their skills.
Why Choose Ethical Hacking Coaching Near Sangam Vihar Bus Depot
For students in South Delhi, accessibility and convenience are key. EINITIAL24’s Sangam Vihar center is strategically located near the Sangam Vihar Bus Depot, making it easy to reach by multiple bus routes. The area is also connected to the Delhi Metro network: the nearby Govind Puri station (Magenta Line) and Malviya Nagar station (Yellow Line) are within a short drive or a reasonable walk from the bus depot. This means students from across Delhi — from Saket, Hauz Khas, Neb Sarai or Tughlakabad — can commute efficiently to our institute. The proximity to Jamia Millia Islamia and Jamia Hamdard (just north of Sangam Vihar) also makes it convenient for college students to drop by after classes. For local residents, choosing an institute close to home has obvious benefits: lower travel time, cost savings, and the comfort of studying in a familiar neighborhood.
Being near the South Delhi campus has another advantage: flexibility. Students often juggle school, college, or jobs with upskilling. Our institute offers flexible batch timings — weekday evenings and weekend slots — to accommodate diverse schedules. Whether you’re a college student or a working professional, you can find a batch that fits your routine. Moreover, as a cyber security institute near Sangam Vihar Bus Depot, we cater specifically to local students’ needs. We understand the local talent pool and the kinds of employers in the region, so we tailor practical exercises and workshops accordingly. In short, if you’re searching for “ethical hacking institute in Sangam Vihar” or “best ethical hacking classes near me,” EINITIAL24 provides an ideal solution — combining location convenience with high-quality training.
Benefits of Local Training Institutes
Choosing a local training institute has several perks:
- Easy Commuting — You save precious time and money by not traveling across the city. This allows more time for study and practice.
- Personalized Attention — Smaller local institutes often keep batch sizes limited, so trainers can give more one-on-one guidance.
- Community Learning — Training with peers from your neighborhood creates a support network. You can study together, share resources, and form study groups.
- Immediate Clarification — In an offline class, you can ask questions in real time. This boosts understanding, especially for complex ethical hacking topics.
- Rapid Response to Queries — Many local centers (including EINITIAL24) maintain active student groups and can answer doubts even outside class hours.
By contrast, purely online courses may offer flexibility, but they lack hands-on lab facilities and peer interaction. At a local institute, you benefit from real computers and networking equipment on-site. This is crucial in ethical hacking, where practicing on physical networks and hardware can’t be fully replicated virtually. In our Sangam Vihar lab, for example, students work on multiple dedicated machines running Kali Linux, testing routers and switches, and simulating Wi-Fi and IoT environments. This practical lab-based learning cements your skills much more effectively than watching a webinar alone.
Weekend & Weekday Batch Availability
We understand that many students and professionals have daytime commitments. That’s why we offer both weekday and weekend batches for our ethical hacking courses. Weekday batches typically run in the evenings (for example 7–9 PM on weekdays), which is perfect for college students or office-goers. Weekend batches run Saturday and Sunday daytime, enabling intensive multi-hour sessions for those who prefer to learn in a consolidated format. The syllabus remains the same; only the schedule differs. Weekend batches can be especially fast-paced, covering more material in fewer weeks, which is great if you want a shorter course duration. Our flexible scheduling is one of the reasons local students seek out EINITIAL24 — we fit training into your life, not the other way around.
Practical Lab-Based Learning
Hands-on practice is the cornerstone of any ethical hacking training. In our Sangam Vihar center, every concept taught in theory is immediately reinforced with lab exercises. Students get to perform real penetration tests in controlled environments. For example, after learning about network scanning, you’ll use tools like Nmap on actual routers to map open ports. After studying SQL injection, you’ll attack a sample web application prepared for training. These labs include tasks like cracking passwords, sniffing network traffic with Wireshark, launching simulated Denial-of-Service attacks, and practicing evasion techniques. In addition, we run Capture The Flag (CTF) style challenges regularly — these are gamified hacking competitions where you solve problems to find “flags” hidden in vulnerable systems. CTFs are widely regarded as an effective way to build practical skills, since they mimic real-world hacking scenarios in a fun, team-based format. At our institute, you’ll often work in small teams on CTF challenges, which boosts learning and teamwork abilities. This emphasis on real-time, lab-based training means graduates of EINITIAL24 aren’t just theoretically knowledgeable — they can actually hack systems (ethically) under pressure, a skill highly prized by employers.
What You Will Learn in an Ethical Hacking Course
An ethical hacking course covers a broad range of skills and topics. You will learn:
- Networking and System Fundamentals: Basic computer networking (TCP/IP, DNS, HTTP), Linux/Windows administration, and how operating systems work. These fundamentals are essential before jumping into hacking techniques.
- Footprinting and Reconnaissance: Techniques for gathering information about targets (companies, websites, networks) without being detected. This includes using search engines, public databases, social media, and DNS/WHOIS tools.
- Scanning and Enumeration: Methods to scan networks for live hosts, open ports, services, and system details. Tools like Nmap and Nessus are used to identify potential vulnerabilities.
- Vulnerability Analysis: How to analyze systems and networks for security holes. This includes running vulnerability scanners and interpreting results to prioritize threats.
- System Hacking: Strategies attackers use to gain unauthorized access to systems (e.g. password cracking, buffer overflows). You will learn countermeasures and practice gaining administrator-level access on test machines.
- Malware Threats: Understanding malware (viruses, trojans, ransomware) and how to analyze malicious code. This module covers static and dynamic analysis of malware samples.
- Sniffing and Network Attacks: Using packet-sniffing tools (like Wireshark) to intercept data, ARP poisoning to trick switches, and hijacking network traffic. You’ll also learn defenses against these attacks.
- Social Engineering: Techniques that exploit human psychology (like phishing, baiting, pretexting). You will simulate phishing attacks in a lab to see how easy it can be to compromise credentials.
- Web Application Hacking: Testing websites and web services for vulnerabilities (including OWASP Top 10 risks). You’ll practice SQL injection, cross-site scripting, and use tools like Burp Suite for automated scanning.
- Wireless Network Hacking: Attacking Wi-Fi networks (WEP, WPA/WPA2) to crack encryption, and discovering rogue access points. Real wireless routers and adapters are used in the lab.
- Mobile and IoT Hacking: Exploring vulnerabilities in Android/iOS apps and IoT devices. This includes attacking mobile devices via ADB, APKs, and testing internet-connected gadgets.
- Cloud and IoT Security: Securing cloud deployments and IoT ecosystems. You’ll learn how cloud misconfigurations (like open storage buckets) can be exploited.
- Denial-of-Service Attacks: Simulating DoS/DDoS attacks and understanding mitigation. This often involves setting up bots or using stress tools on test servers.
- Cryptography and Countermeasures: The basics of encryption algorithms, how public-key infrastructure works, and common crypto attacks. You’ll learn to use encryption tools and how to break weak ciphers.
Throughout the course, practical lab sessions use industry-standard tools. For instance, we use Kali Linux — a specialized security-focused Linux distribution — as the main hacking platform. Tools like Nmap (network scanner), Wireshark (packet analyzer), Burp Suite (web app proxy), Metasploit (exploit framework), John the Ripper (password cracker), and Aircrack-ng (Wi-Fi cracking tool) are integrated into exercises. By course end, you will be fluent in using these tools to test and secure real systems. EINITIAL24’s curriculum ensures you not only understand the theory of each topic, but have actually used the tools against vulnerable targets in our lab environment.
Ethical Hacking Course Modules
Our ethical hacking training follows a structured module-based syllabus, covering all the necessary domains. Typical modules include:
- Introduction to Ethical Hacking: Concepts of security, threat levels, hacker ethics, and legal aspects.
- Footprinting & Reconnaissance: Passive and active data gathering (whois lookup, Google hacking, social networks, dark web OSINT).
- Scanning Networks: Port scanning, host discovery, service detection, and scanning beyond simple tools to evade firewalls.
- Enumeration: Listing network resources and users (SMB, LDAP, SNMP enumeration, etc.) to find entry points.
- Vulnerability Analysis: Using scoring systems (like CVSS) and databases (CVE, NVD) to prioritize vulnerabilities, plus automated scanning tools.
- System Hacking: Techniques to break into Windows and Linux systems — password cracking, privilege escalation, backdoors, and maintaining access.
- Malware Threats: Practical labs on how Trojans, viruses, worms, and ransomware work. Malware analysis and sandboxing methods are taught.
- Sniffing & Packet Analysis: Capturing network traffic, analyzing packets, and countermeasures like ARP poisoning prevention and securing networks.
- Social Engineering: Simulated phishing campaigns, impersonation tactics, and training on setting up physical and digital decoys (honeypots).
- Denial-of-Service Attacks: Simulating simple DoS tools and larger DDoS scenarios in a controlled setup, then learning mitigation (rate limiting, filtering).
- Session Hijacking: Exploiting web sessions (cookie theft, replay attacks) and techniques to secure sessions.
- Evading IDS/Firewalls/Honeypots: Learning how attacks can bypass common network defenses and how to detect and prevent such evasion.
- Web Server Hacking: Attacks on server software — finding misconfigurations, directory traversal, DNS spoofing, and securing web server configurations.
- Web Application Hacking: Detailed exploration of web vulnerabilities (SQLi, XSS, CSRF, file upload flaws) and countermeasures such as input validation and WAFs.
- SQL Injection: Hands-on SQL injection attacks on test databases (MSSQL, MySQL), covering error-based, union-based, blind, and bypass techniques.
- Wireless Network Hacking: Cracking WEP/WPA keys, performing MITM attacks on Wi-Fi, and securing wireless access points.
- Hacking Mobile Platforms: Attacks specific to Android and iOS (reverse engineering APKs, exploiting ADB, jailbreaking, mobile phishing) and securing mobile apps.
- IoT and OT Hacking: IoT architecture, embedded device attacks, ICS/SCADA vulnerabilities, and how to secure smart devices.
- Cloud Computing: Attacks on AWS/Azure/GCP (misconfigured buckets, identity flaws), container (Docker/Kubernetes) vulnerabilities, and cloud security best practices.
- Cryptography: Encryption algorithms (AES, RSA), hashing, digital signatures, and cryptanalysis basics (breaking weak ciphers and certificate attacks).
Each module blends theory with hands-on labs. For example, in the “Malware” module you’ll actually write a benign Trojan to infect a test virtual machine, then dissect how it operates. In “Wireless Hacking,” you’ll set up a Kali Linux machine with a wireless adapter and crack the WPA2 password of a dummy AP you configure. This exhaustive module lineup ensures that graduates of our course have covered all the topics expected in global certifications and job roles.
Who Can Join Ethical Hacking Coaching?
Ethical hacking is a versatile field open to many backgrounds. You can join our courses if you are:
- A recent 12th-grade graduate with an interest in computers. Even without a formal degree, motivated beginners can pick up the basics quickly.
- A college student (engineering, IT, computer science, or even other streams) looking to add cybersecurity skills alongside your major. Many students pursue hacking courses to boost their placement opportunities.
- A working IT professional who wants to transition into security. Even if you’re already in networking or system administration, an ethical hacking course will add valuable skills to your profile.
- Beginners interested in cybersecurity, even with no prior coding or advanced computing background. The only prerequisites are basic computer literacy and willingness to learn. We start from fundamentals so you don’t need to know programming at the start (though learning Python or scripting later is encouraged).
- Network Engineers & System Administrators who want to strengthen network security. If you manage servers or networks, ethical hacking training teaches you how attackers will try to compromise those systems, so you can defend them better.
- Anyone with a curious, analytical mindset — ethical hacking is a skill-driven field. If you enjoy puzzles, logical challenges, and understanding how things work under the hood, you’ll fit right in.
Importantly, no advanced coding skills are required to start. Many students begin their journey in ethical hacking without prior programming knowledge. Over the course, you’ll pick up necessary scripting basics (e.g. Python or Bash for writing simple tools), but our trainers will guide you through this. According to cybersecurity educators, even absolute beginners can learn ethical hacking within 3–6 months. With consistent effort, you’ll gain proficiency in the core concepts and tools by the end of the program.
Ethical Hacking Certifications You Can Prepare For
Our courses at EINITIAL24 prepare you for leading industry certifications, which validate your skills to employers. Some key certifications include:
- Certified Ethical Hacker (CEH) — Offered by EC-Council, CEH is one of the most recognized certifications worldwide for penetration testers. Our curriculum aligns with the CEH syllabus, so students can sit for the CEH exam after training. Having CEH on your resume often attracts recruiters.
- CompTIA Security+ — A popular entry-level security certification. It covers fundamental security concepts and is valued by many organizations.
- Computer Hacking Forensic Investigator (CHFI) — Also from EC-Council, CHFI focuses on cyber forensics — tracing intrusions and recovering evidence. If you’re interested in incident response careers, CHFI is an excellent choice.
- CompTIA PenTest+ — This certification is focused specifically on penetration testing techniques, similar to CEH. It’s a good complement for hands-on professionals.
- OSCP (Offensive Security Certified Professional) — A very challenging, hands-on certification for advanced penetration testers. While OSCP is premium, our training provides a stepping stone by covering many of its required skills.
Beyond these, our institute can guide you toward other certifications like CISSP (for security management roles), Cisco’s CCNA Security (for network security), and specialized certificates (Cloud+ for cloud security, CISM, etc.) depending on your career goals. Importantly, when you join us, trainers give tips and practice exams for each certification. For example, CEH requires understanding five phases of hacking; we prepare you thoroughly for those exam objectives. Our past students have successfully earned CEH, CHFI, and Security+ certificates and then leveraged them into jobs. In short, your training at EINITIAL24 will not only teach you how to hack ethically, but also how to prove your skills with official certifications.
Course Duration and Training Options
We offer flexible course durations to suit your needs:
- 3-Month Intensive Program — A faster-paced option, typically involving daily or alternate-day classes. Suitable if you can dedicate full-time effort for a short period.
- 6-Month Regular Program — The standard format, with classes 2–3 times per week. Ideal for balancing with college or work.
- Fast-Track Training — If you want to finish even sooner, we offer accelerated weekend-only or daily batches that compress the syllabus.
- Weekend-Only Batches — Classes on Saturdays and Sundays. This suits working professionals who cannot attend weekday classes at all.
- Online + Offline Hybrid Options — For those who prefer some remote learning, we provide recorded sessions and live online classes in addition to classroom labs. (Students often start with online theory and then come to the center for labs.)
Regardless of format, the total content covered is the same. You can switch batches if needed, and our trainers also offer doubt-clearing sessions outside class hours. We understand learners have different paces: whether you are a quick learner aiming for OSCP or someone who needs more practice on basics, we have a track that fits you. In general, expect to invest 60–100 hours of instruction in a 3-month course, and around 120–150 hours in a 6-month course. Homework and lab work outside class are also assigned for practice.
Classroom Training
Our core offering is classroom (in-person) training. In our Sangam Vihar classrooms, you’ll learn directly from certified cybersecurity instructors who have real-world hacking experience. They demonstrate techniques live on projectors, then supervise as you repeat the steps on your computer. The classroom environment encourages questions and discussions — if one student raises a doubt, the trainer can address it for everyone. We maintain a low student-to-instructor ratio so that each student gets personal guidance. Our labs are equipped with high-performance PCs running multiple virtual machines, networking gear (routers, switches), and Wi-Fi setups. This on-site facility is a big advantage over self-study; you can see and feel the hardware.
Online Live Sessions
For students who cannot always be physically present, we also offer live online classes via video conferencing. These sessions cover the same syllabus but allow remote participation. You’ll need a stable internet connection and a laptop/desktop to follow along. During online sessions, the instructor shares their screen (showing lab exercises) and you follow on your own machine. You can ask questions by chat or voice, and our trainers are attentive to remote students’ queries. Online batches still maintain small groups for interaction. We also provide digital lab access — you’ll get VPN credentials to log in to our cloud labs where you can practice the same exercises we do on-site. This ensures you don’t miss the hands-on component even if you’re off-campus.
Hybrid Learning Model
Our hybrid model combines the best of both worlds. For example, you might attend theory lectures online during the week and come to the lab once a week for practical sessions. Or you might watch recorded videos for some modules and do a live workshop for others. This flexibility is especially helpful for advanced students who want to learn at their own pace in some areas but still need hands-on practice. We encourage students to mix and match — many join online first and then switch to in-person labs when ready. With a hybrid plan, you also get lifetime access to online course materials and recorded videos, so you can review modules anytime after class.
Ethical Hacking Course Fees Near Sangam Vihar Bus Depot
Ethical hacking course fees can vary widely depending on the institute and the level of training. In Delhi, entry-level courses might start around ₹15,000–₹25,000 for a basic package (covering core modules and hands-on labs). More comprehensive or advanced training (including extras like extended lab access, fast-track batches, or one-on-one mentoring) might range from ₹40,000 up to ₹80,000 or more. Some institutes charge even higher for premium courses. At EINITIAL24, we aim to keep fees competitive without compromising quality. We offer flexible payment options, including no-cost EMIs, so that you can spread the cost over several months. Certification exam fees (like the CEH exam voucher) are usually extra and paid directly to certifying bodies.
To illustrate, one survey of ethical hacking courses reports fees typically falling between ₹10,000 and ₹2,50,000 in India, depending on duration and syllabus. The actual fee you’ll pay also depends on factors like course format (online vs offline), whether study materials are included, and any extra perks (career services, placement assistance). We make all fee structures transparent upfront. For example, our 3-month classroom ethical hacking course currently starts at around ₹20,000, which includes all classroom training, lab usage, and study materials. Advanced or accelerated courses with guaranteed placement support may cost more.
Tools Used During Ethical Hacking Training
As part of training, we introduce students to the most widely-used security tools in the industry. Examples include:
- Kali Linux: A Debian-based operating system loaded with hundreds of hacking and security tools. We use Kali on all lab machines.
- Nmap: A powerful network scanner used to discover hosts and services on a computer network.
- Wireshark: A packet analyzer that lets you capture and interactively browse the traffic running on a computer network.
- Burp Suite: An integrated platform for testing web application security (intercepts and modifies HTTP traffic).
- Metasploit Framework: A tool for developing and executing exploit code against a remote target.
- John the Ripper: A fast password cracker for testing password strength and recovery.
- Aircrack-ng: A suite of tools for auditing wireless network security (used to crack WEP, WPA/WPA2).
These tools (and many others) are not only taught but used in extensive practical exercises. For instance, students practice scanning with Nmap to map an entire virtual network, or use Metasploit to exploit known vulnerabilities in a deliberately weak web server we set up. The emphasis is on hands-on mastery — knowing what these tools do and how to interpret their output. In each case, instructors also cover the countermeasures and ethical considerations, so you learn how to defend systems against the very techniques you’re practicing.
Career Opportunities After Ethical Hacking Training
Completing an ethical hacking course opens many career paths in cybersecurity. Some common job roles include:
- Ethical Hacker/Penetration Tester: Directly responsible for simulating attacks to find security weaknesses. This is often the first role people think of in this field.
- Security Analyst: Monitoring networks and systems to detect attacks, respond to incidents, and improve defenses. Security analysts often work in SOCs (Security Operations Centers).
- SOC (Security Operations Center) Analyst: A specialized security analyst focused on triaging and investigating security alerts 24/7 in shift rotations.
- Cybersecurity Consultant: Advising organizations on best security practices, doing risk assessments and audits. Consultants may be employed by firms or freelance.
- Incident Response Specialist: Handling security breaches when they occur — analyzing the attack, containing it, and planning recovery. They often have forensic skills.
- Network Security Engineer: Designing and maintaining secure network infrastructure, including firewalls, IDS/IPS systems, and VPNs.
- Security Auditor: Ensuring compliance with security policies and regulations, often performing scheduled pentests to meet audit requirements.
- Forensic Investigator: After an incident, gathering evidence and tracing the attacker’s steps. This is closely related to incident response.
- Cybersecurity Trainer/Educator: Senior ethical hackers often become trainers themselves, teaching the next generation of hackers.
These roles exist across industries — from IT companies and banks to telecoms and government agencies. Demand for entry-level positions is especially high in security operations and penetration testing. Many EINITIAL24 alumni have joined companies as junior pentesters or analysts, and later moved up to senior security roles or consulting positions. With experience, one can advance to roles like Security Architect or even CISO (Chief Information Security Officer), though those usually require additional management skills.
Freelancing is also an option — many ethical hackers do bug bounty hunting or offer pentesting services on contract. In India, freelance ethical hackers can earn significantly, sometimes exceeding salaries of full-time roles, depending on the clients they serve.
Expected Salary After Ethical Hacking Course
After certification and a bit of experience, you can expect a rewarding salary trajectory. Roughly speaking:
- Entry-level (Freshers): ₹4–7 LPA. Many freshers with a certification like CEH or Security+ start in this range.
- Mid-level (3–5 years experience): ₹8–15 LPA. As you gain hands-on experience and possibly higher certs (like OSCP or CISSP), salaries climb.
- Experienced (5+ years): ₹20 LPA and above. Senior penetration testers, security engineers, or managers often earn 20+ lakhs. Those with specialized skills (cloud security, threat intelligence) or leadership roles can see ₹30–40 LPA or more.
Specialized tracks can command even higher pay. For instance, AWS/Azure security architects can earn well into the ₹30+ LPA range in 2026. Government roles typically pay on the lower side of these ranges but have excellent job security and benefits. In all cases, being certified and skilled gives you leverage in negotiating salary. The bottom line is that the return on investment for an ethical hacking course is very high: even at the lower end, ₹5–6 LPA for a starting job is on par with or better than many other IT fields in India.
Placement Support and Internship Opportunities
Choosing the right training institute can greatly influence your job prospects. At EINITIAL24, we emphasize career support just as much as technical training. Our placement assistance includes:
- Resume Building: We help you craft a compelling cybersecurity-focused resume, highlighting your project work and certifications.
- Mock Interviews: We conduct practice technical interviews and HR interviews to prepare you for common questions that employers ask. This includes problem-solving and practical tests.
- Internship Guidance: We partner with local companies and startups to facilitate internship opportunities. During your course, we encourage real-world projects and connect interested students with short-term internships in security.
- Industry Networking: We organize guest lectures and meetups with industry professionals (ethical hackers, CISOs, cybersecurity startups). These events often lead to referrals and job leads.
- Real-World Projects: Our courses include capstone projects (like pentesting a simulated corporate network). You can showcase these in your portfolio. We also mentor students on contributing to open-source security tools or writing vulnerability reports (bug bounties) as portfolio pieces.
- Placement Assistance: Finally, after course completion, our placement cell shares job openings with you, arranges interview drives with hiring partners, and guides you through the application process. Many students receive interview calls from MNCs and startups through our network.
While we cannot guarantee a job (no legitimate institute can), our track record shows high placement rates. Most students begin applying to roles while still in training, armed with new skills and certifications. Having an institute like EINITIAL24 on your resume signals to employers that you have undergone rigorous training. Many employers in Delhi prefer candidates who trained at recognized institutes for ethical hacking, particularly for junior security roles.
How to Choose the Best Ethical Hacking Institute Near Sangam Vihar Bus Depot
With multiple options available, selecting the right training center is crucial. Here are key factors to look for:
- Experienced Trainers: Instructors should be certified professionals (CEH, CISSP, OSCP, etc.) with real-world cybersecurity experience. Ask about their backgrounds. Trainers who have worked on actual cyber attacks or large-scale security projects bring invaluable insights.
- Hands-On Labs: The institute must have dedicated lab infrastructure — multiple systems, networking devices, IoT gadgets, etc., so every student can practice. Pure theory classes are not enough; ensure that your training includes extensive lab time.
- Placement Assistance: Check if the institute offers resume help, interview prep, and industry tie-ups. Read reviews or ask alumni about their placement support. An institute that promises placement is better than one that leaves you on your own after classes.
- Certification Focus: A good institute aligns its syllabus with official certifications (like CEH). See if they provide exam vouchers or official study materials. Preparing under an institute’s guidance often increases your chances of passing certification exams.
- Student Reviews: Look up testimonials or reviews. Satisfied students often mention how the course helped them get hired. Beware of gimmicky promises; genuine feedback tends to detail what students learned.
- Demo Classes: Many institutes offer a free demo class or trial session. Use this opportunity to gauge the teaching style and environment. Make sure you find the instructor clear and the pace appropriate.
- Updated Syllabus: Cybersecurity changes constantly. Ensure the course content is up-to-date with the latest attack techniques (for example, modules on IoT security, cloud hacking, AI threats). Institutions should update their curriculum regularly.
- Batch Size: Smaller batches mean more attention. Ask how many students are in each class. Large lecture-style classes may not give you enough lab time.
- Mode of Training: Decide if you need purely offline, purely online, or hybrid. If mobility is an issue (e.g., during COVID or other constraints), check the quality of online instruction.
EINITIAL24 excels on all these criteria. Our trainers hold multiple security certifications and 5+ years in the field. We continually update our labs (adding new exploits and scenarios every quarter). We have a high student satisfaction rate, and many graduates return for advanced courses. Prospective students are always welcome to attend a free demo or audit one class. We emphasize practical learning and career readiness, which sets us apart from purely theoretical programs.
Online vs Offline Ethical Hacking Coaching
When choosing an ethical hacking course, you may consider whether to learn online or offline. Each has advantages:
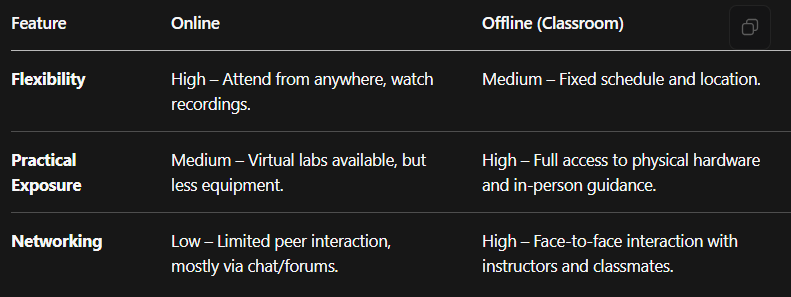
Online training offers the greatest flexibility. You can take classes from home or office, and recordings mean you never miss a lecture. This is ideal if you travel or need a fully remote schedule. However, online students must be self-disciplined, and they miss out on the energy of a live lab environment. Offline (in-class) coaching requires commuting, but in return you get immediate help, real lab infrastructure (multiple machines per student), and easier collaboration with classmates on complex tasks. Networking with fellow security enthusiasts is often easier in person. Many learners choose a hybrid approach: they attend online theory lectures to save time, but still come to physical labs on weekends or for specific workshops.
Our experience at EINITIAL24 is that offline classes maximize learning for ethical hacking. We see students progress faster when they can ask the trainer to directly help on their screens, or spot something new when watching a live demo. However, we ensure our online students aren’t left behind: our online sessions use high-resolution screen-sharing and live chat, and we give virtual lab access so remote students complete the same exercises. Ultimately, the “best” mode depends on your personal needs — but remember, regardless of mode, the focus should be on practical exercises rather than just lectures.
Why Practical Training Matters in Ethical Hacking
Ethical hacking is a skill best learned by doing. Theory can give you knowledge of attacks, but only hands-on practice will make you proficient. That’s why practical training is so crucial:
- Real-Time Labs: Working in a lab lets you experience real attack/defense scenarios. For instance, launching a simulated ransomware attack on a virtual machine helps you understand how such malware spreads and how to stop it.
- Capture The Flag (CTF) Challenges: CTFs are live competitions where you solve security problems to find hidden “flags”. They teach you to think on your feet and apply skills in varied contexts. Most institutes, including ours, incorporate CTF exercises because they mimic real-world problem-solving. For beginners, CTFs provide a safe playground to learn from mistakes.
- Simulated Attacks: We use “cyber ranges” (sandboxed environments) to simulate real corporate networks. You might “hack” one part of our network, then move laterally to another segment. This builds intuition on how attackers behave. It also lets you practice incident response — for example, cleaning up after your own mock attack.
- Industry Scenarios: Our labs often replicate common business setups (e.g., an online bank network, a hospital’s Wi-Fi). This context helps you understand how security issues can impact actual organizations.
- Soft Skills: Practical sessions improve more than just technical skills. Working in teams during labs teaches communication and collaboration — vital abilities in security jobs.
- Employer Confidence: Employers strongly prefer candidates who can demonstrate real hacking experience. In fact, some certifications (like the CEH practical or OSCP) require you to perform actual exploits in a controlled test environment. By training on real tools and systems, you prove your skills.
In summary, practical experience is what turns a theoretical learner into a competent ethical hacker. As one cybersecurity educator noted, ethical hacking courses provide “live cyber range experience and CTF-style challenges which simulate actual cyber attacks”. When you complete our training, you won’t just “know” about vulnerabilities — you will have exploited them and then patched them. This practical confidence is why our students are job-ready from day one.
FAQs About Ethical Hacking Coaching
Q: What is the best ethical hacking coaching near Sangam Vihar Bus Depot?
A: For students in South Delhi, EINITIAL24 is highly recommended. Our Sangam Vihar center specializes in ethical hacking and cyber security training, with experienced instructors and well-equipped labs. You can visit us at the Sangam Vihar Bus Depot area for a free demo class.
Q: Which institute offers ethical hacking classes with placement in Delhi?
A: EINITIAL24 offers comprehensive placement support along with its courses. We assist with resume building, mock interviews, and connect students to industry internships and job openings in Delhi’s cybersecurity market.
Q: What is the fee for ethical hacking coaching near Sangam Vihar?
A: Course fees vary by program. As a guideline, entry-level ethical hacking courses in Delhi range roughly ₹15,000–₹25,000. Advanced or extended programs can go up to ₹40,000–₹80,000, depending on included features. Please contact EINITIAL24 for current fee details. We also provide EMI payment options to make the fees manageable.
Q: Can beginners join an ethical hacking course without coding knowledge?
A: Absolutely. Beginners are welcome. Our courses start with the basics of networking and security concepts, and we teach required scripting (like Python or Bash) from the ground up. Students with general computer knowledge (like familiarity with Windows and internet usage) can start right away. In fact, ethical hacking can be learned in 3–6 months even by those new to IT.
Q: What is the duration of an ethical hacking certification course?
A: It depends on the program. Standard courses often run 3 to 6 months. Accelerated or part-time courses may be completed in as little as 1–2 months of full-time study or in 6–12 months of part-time study. EINITIAL24 offers flexible batch options, including fast-track weekend-only classes to fit your schedule.
Q: Which ethical hacking certification is best for beginners in India?
A: For beginners, the CEH (Certified Ethical Hacker) and CompTIA Security+ are very popular certifications. CEH is widely recognized and focuses on practical hacking tools and techniques. Security+ covers broader cybersecurity fundamentals and is also well-regarded. After those, you might pursue specialized certs like CompTIA Pentest+ or CHFI as you progress.
Q: Is ethical hacking a good career option in 2026?
A: Yes. Ethical hacking remains a top career choice in 2026 due to high demand and growing cyber threats. It is considered recession-resistant and offers strong salary potential. Cybersecurity experts often enjoy better pay hikes than many other IT fields. If you have an interest in cybersecurity, ethical hacking is an excellent path with global opportunities.
Q: What skills are required to become an ethical hacker?
A: Key skills include understanding of computer networks (TCP/IP), operating systems (especially Linux), and basic programming or scripting. You should be curious, analytical, and persistent (often described as having a “hacker mindset”). Soft skills like critical thinking and communication are important too. However, you can acquire these skills during training; most institutes will teach you the technical foundations from scratch.
Q: Does ethical hacking coaching include practical lab training?
A: Yes — practical lab training is essential in ethical hacking courses. At EINITIAL24 and other good institutes, every topic is paired with hands-on exercises. You will use tools like Kali Linux, Metasploit, Wireshark, etc., on real or virtual networks. Expect regular lab sessions and simulated cyberattacks as part of your coursework.
Q: What are the job opportunities after completing an ethical hacking course?
A: After finishing the course, you can apply for roles such as Penetration Tester (Ethical Hacker), Security Analyst, SOC Analyst, Cybersecurity Consultant, Incident Response Specialist, or even roles in IT audit and forensics. Many industries hire for these positions. EINITIAL24 also works with hiring partners, so you’ll have guidance on where to apply.
Q: Can I learn ethical hacking after 12th grade?
A: Yes, you can start learning ethical hacking right after 12th grade. Many students enroll in certificate or diploma courses in cybersecurity immediately after high school. Our Sangam Vihar center has helped numerous young students begin their cybersecurity education at that stage. As long as you have basic computer skills and interest, you can join.
Q: Which is better for ethical hacking training: online or offline classes?
A: Both formats have pros and cons. Online classes offer high flexibility (you can learn from anywhere and often on your own schedule) but require self-discipline and may offer less direct lab support. Offline (in-person) classes provide more hands-on guidance, better lab access, and peer learning, but require you to travel to the center. At EINITIAL24, we offer hybrid options to get the best of both. For beginners, in-person training is often recommended to build a strong practical foundation.
Q: What tools are taught in ethical hacking coaching institutes?
A: Common tools include Kali Linux (the hacking OS) with built-in tools, Nmap (network scanner), Wireshark (packet sniffer), Burp Suite (web testing proxy), Metasploit (exploit framework), John the Ripper (password cracker), Aircrack-ng (wireless hacking), Nikto, OWASP ZAP, and many others. A good course will introduce at least the top 10–15 tools used by professionals.
Q: Do ethical hacking institutes provide internship opportunities?
A: Many reputable institutes do offer help with internships. At EINITIAL24, we connect students with internship programs at partner companies, so you can apply what you’ve learned in a real environment. Internships can even lead to full-time job offers if you perform well.
Q: What is the average salary of a certified ethical hacker in India?
A: On average, a certified ethical hacker in India earns around ₹5–7 lakhs per year as a starting salary. With a few years’ experience and additional certifications, this can rise significantly (often ₹15–20 lakhs or more). Salaries vary by city and industry, but in metro areas like Delhi, competitive packages are common.
Q: How do I choose the best cyber security institute near me?
A: Look at factors like trainer experience, lab facilities, placement support, and student feedback. Visit potential institutes, ask about their syllabus, and see if they offer a trial class. For South Delhi, EINITIAL24’s Sangam Vihar branch is a strong option given its track record and up-to-date curriculum.
Q: Is CEH certification included in ethical hacking coaching programs?
A: Many institutes design their course around the CEH syllabus, so they teach everything you need to know for the CEH exam. However, taking the official CEH exam is usually optional. At EINITIAL24, we do provide CEH exam preparation and can help you register for the exam, but the exam fee is separate. Our focus is on building the skills; actual certification depends on your exam attempt.
Q: Are weekend ethical hacking classes available near Sangam Vihar Bus Depot?
A: Yes. EINITIAL24 offers weekend batches specifically to accommodate local working professionals and college students. Weekend classes typically run for longer hours (e.g., 4–5 hours each on Saturday/Sunday) to cover the week’s lessons. This is convenient if you cannot attend weekday classes.
Q: What is the difference between cyber security and ethical hacking?
A: “Cyber security” is the broad field of protecting networks, systems, and data from attacks. It includes many roles (risk management, compliance, auditing, defense operations, etc.). Ethical hacking (also known as penetration testing) is a specialized discipline within cybersecurity focused on actively probing systems for vulnerabilities by thinking like an attacker. Ethical hackers are part of the cyber security ecosystem but specifically focus on testing and breaking in, whereas other security professionals might be more focused on policy, monitoring, or defensive architecture.
Q: Do ethical hacking coaching institutes offer placement assistance after course completion?
A: Yes. Leading institutes (including EINITIAL24) do provide placement help. This usually includes resume reviews, interview preparation, and connecting students with hiring companies. We emphasize placement as part of our program, sharing job openings and inviting recruiters to our campus. While we cannot guarantee every student gets placed, we actively support your job search.
Final Conclusion
Ethical hacking is a rewarding and future-proof career choice in 2026. With cyber attacks increasing in scale and sophistication, skilled white-hat hackers are in acute demand across all industries. Training in ethical hacking equips you not only with technical know-how, but also with a mindset to think like hackers, which is invaluable for any cybersecurity role.
For students around Sangam Vihar and Tughlakabad in South Delhi, practical, local training is easily accessible. EINITIAL24 offers the right combination of benefits: easy reach from the Sangam Vihar Bus Depot, flexible class schedules, hands-on lab facilities, and strong placement support. Our updated curriculum covers all key modules — from reconnaissance to cryptography — and uses real industry tools (Kali Linux, Nmap, Metasploit, etc.) so you gain genuine expertise.
By joining EINITIAL24’s ethical hacking coaching, you’ll gain not only knowledge but also certifications and real-world experience. We help prepare you for recognized certifications (CEH, Security+, CHFI) and internships, giving you an edge in the job market. Graduates often report securing jobs at IT companies, banks, government agencies, and consulting firms.
Ultimately, cybersecurity is not just a trend but a critical necessity for the digital world. Choosing a practical training program with updated content ensures you are job-ready. If you’re passionate about technology and want a career with strong growth, start your journey now.
Ready to become a skilled ethical hacker? Reach out to EINITIAL24 near Sangam Vihar Bus Depot for more information. Enroll in our next batch, join our hands-on labs, and take the first step toward a high-flying cybersecurity career. Your future in cyber security starts here!